April 1 passes with its usual pranks and hoaxes fading away, but the threat of scams remains ever-present.
Sadly, fraudsters never take a break.
Spring is prime time for cybercriminals—not because employees are careless, but because the fast pace and distractions of the season create openings for deceptive schemes to slip by unnoticed until it's too late.
Here are three current scam tactics targeting vigilant, well-intentioned workers caught in the daily rush.
As you review these examples, pause to consider: Would my entire team recognize and stop these attempts?
Scam #1: Fake Toll or Parking Fee Alerts
An employee receives a text message stating:
"You owe $6.99 for an unpaid toll. Pay within 12 hours to avoid penalties."
The message references a legitimate toll agency—like E-ZPass, SunPass, or FasTrak—matching the employee's state. The fee is low enough to seem harmless.
In-between meetings, the employee clicks the link and pays quickly.
But the link is fraudulent.
In 2024, the FBI logged over 60,000 reports of counterfeit toll payment texts, with complaints surging 900% in 2025. Researchers have uncovered more than 60,000 fake domains imitating state toll authorities—proving this scam's high profitability. Some messages target residents in states lacking toll roads entirely.
The scheme succeeds because a small fee feels low-risk, and most people have recently encountered tolls or downtown parking, making the alert believable.
The safest practice: Authentic toll agencies never demand immediate payment via text links. Train employees to access official websites or apps directly for verification. Additionally, they should never respond to such texts—not even with "STOP"—as replies signal an active phone number inviting more fraud attempts.
Convenience is the lure; strict procedures are the shield.
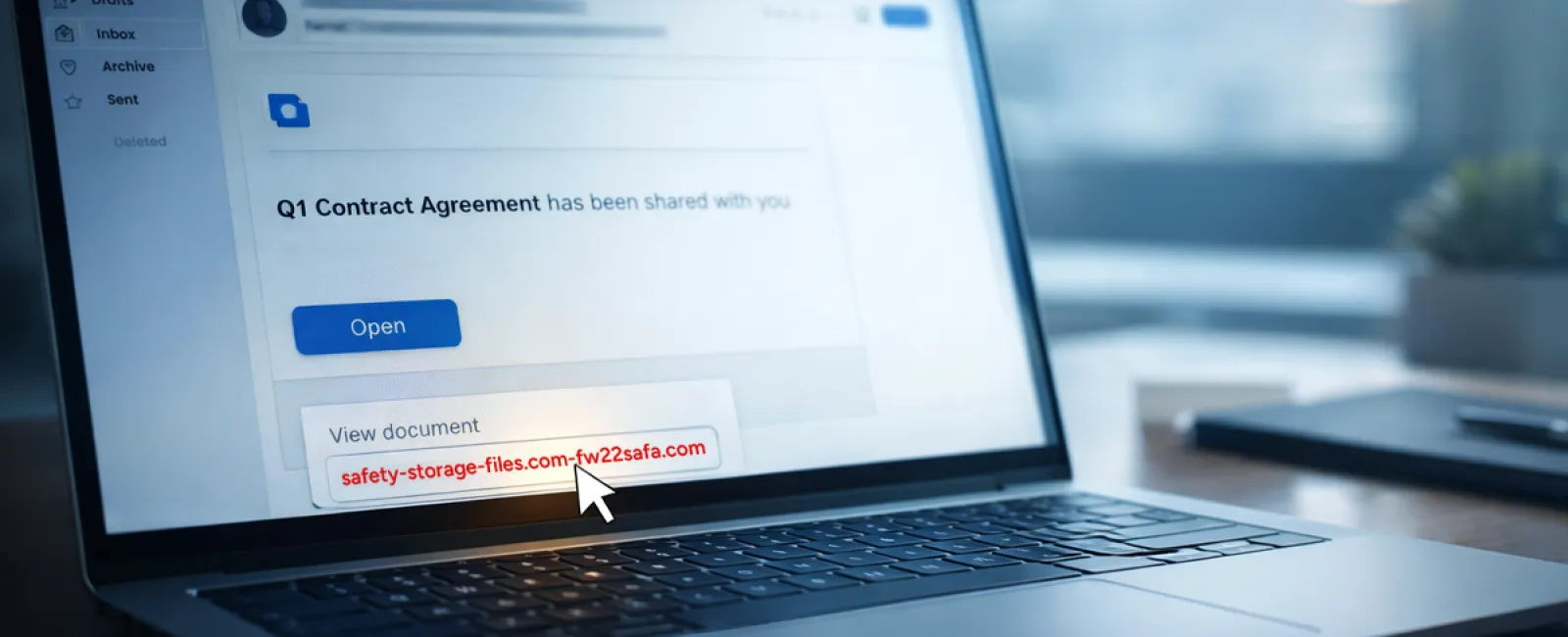
Scam #2: "Your File Is Ready" Email
This scam blends seamlessly into daily workflow.
An employee receives an email claiming a document was shared with them, such as a DocuSign contract, OneDrive spreadsheet, or Google Drive file.
The sender's name looks familiar, and the email formatting mimics authentic file-sharing notifications perfectly.
The employee clicks the link, is prompted to log in, and enters their work credentials.
Now the attacker gains full access to your company's cloud environment.
Phishing campaigns exploiting trusted platforms like Google Drive, DocuSign, Microsoft, and Salesforce jumped 67% in 2025, according to KnowBe4's Threat Labs study. Google Slides phishing links alone surged over 200% in a recent six-month timeframe.
Alarmingly, employees are seven times more likely to click malicious links from OneDrive or SharePoint notifications because they closely resemble legitimate alerts.
Newer tactics go further by using compromised accounts to create and share files, making the phishing email appear as a genuine message from Google or Microsoft servers—evading spam filters.
Defense strategy: Employees should never click unexpected shared file links in emails. Instead, instruct them to log into the platform directly via browser to verify if the file exists. Organizations can minimize threats by controlling external sharing permissions and enabling alerts for unusual login activity—security measures your IT team can set up in minutes.
Simple caution produces powerful protection.
Scam #3: Sophisticated Phishing Emails
Gone are the days of clumsy phishing emails with poor grammar and odd formatting.
Today, AI-generated phishing messages achieve a 54% click rate compared to only 12% for those written by humans, according to a 2025 study.
These emails are crafted to appear legitimate, referencing real companies, job titles, and processes scraped rapidly from LinkedIn and corporate websites.
Attackers target departments selectively: Human Resources and payroll teams receive faux employee verification requests; Finance teams get fake vendor payment change notices. In one recent experiment, 72% of employees clicked vendor impersonation emails—90% higher than other phishing types.
These messages are calm, professional, urgent but not alarmist—just like a typical workday email.
Protective step: Any requests involving credentials, payment changes, or sensitive data must be verified through a second channel, such as a phone call, chat, or face-to-face confirmation. Before clicking links, encourage employees to hover over sender addresses to confirm authenticity. Also, treat urgent emails as red flags warranting extra scrutiny.
Effective security empowers without causing panic.
Key Takeaway
All these scams bank on familiarity, authority, timing, and the "it'll only take a second" mentality.
The real vulnerability lies not in careless employees but in systems expecting everyone to pause, verify, and make flawless decisions under pressure.
When one rushed click can disrupt your entire day, the problem is with process, not people.
And luckily, process problems can be fixed.
How We Support You
Business owners don't want cybersecurity to become a burdensome side project or feel responsible for endless warnings about phishing.
They want assurance that their operations aren't silently at risk.
If you're concerned about your team's vulnerability—or know another owner who should be—let's have a conversation.
Book a straightforward discovery call where we'll cover:
• The current cyber risks impacting businesses like yours
• Common ways threats infiltrate through routine work activities
• Practical strategies to lower your exposure without hindering productivity
No pressure. No fear tactics. Just an honest discussion to identify risks and explore solutions.
Click here or give us a call at 702-896-7207 to schedule your free 15-Minute Discovery Call.
If this doesn't apply to you, feel free to share with someone who could benefit. Awareness transforms a "would have clicked" into a "blocked attempt."